Disclaimer: This post is sponsored by PSECU, a Pennsylvania-based credit union.
Identity theft has always been a frightening concept — but now, with our whole lives displayed on the internet, we’ve become even more vulnerable. Scammers and hackers are getting smart — fortunately, so is protective technology.
Industry-specific technologies work against identity thieves in numerous ways and make it much harder for them to successfully steal your information. Take a look at a few of the top ways technology can safeguard your identity.
-
Encryption
During encryption, your credit card information is changed at the time and point of sale. Then, the data gets encrypted again before being sent to the bank to process your payment. This process makes it impossible for hackers and identity thieves to track your numbers and assemble the information needed to steal your identity.

-
Chip Technology
Chip technology was introduced back in 2015. Many of us remember the switch, but do you know why credit card companies swapped a strip with a chip? The answer is simple — for security against identity fraud.
These microchip-embedded cards enact a two-step verification process. Upon inserting your chipped card, you must then either enter a four-digit PIN or show a signature — usually on your driver's license or some form of identification — to verify the card is actually yours. This process helps cashiers and clerks know the card you're using is yours, thus protecting against identity fraud.
-
Touch-to-Pay Technology
Apple Pay is an example of touch-to-pay technology. This ability cuts down on the amount of personal information transferred during a purchase. Touch-to-pay allows users to store all of their credit card and banking information on their mobile device. They can then use this device to pay in stores or online without giving their personal banking information to the site they’re buying from. Thus, the process is much more secure and guarded against potential hackers.
A common misconception a lot of people have about touch-to-pay is that your account information is stored on your phone or tablet, which can be susceptible to viruses. This is not the case. Touch-to-pay assigns your device a specific number or code and keeps track of that number. The process is the same for each transaction.
Security measures are also put in place to guard against a potential hacker who has access to your physical phone. Apple Pay and other touch-to-pay technologies are guarded by software that requires either facial recognition or a fingerprint for touch access.
-
Automatic Credit Score and Account Activity Monitoring
The above technologies are proactive measures to keep the identity thieves from ever getting into your account. However, you must still make sure you’re keeping tabs on your credit card activity. Most credit card companies can alert you whenever anyone uses your card. Some, like Discover, send a notification that your card was used through a mobile app — often before you even leave the store! You can set parameters to either get notifications all of the time or only when a certain amount is spent.
Credit reporting agencies like Experian, Equifax and TransUnion have similar reports. These reports can notify you if an inquiry was made using the information for your account. A lot of agencies will also allow you to freeze your account. Then, no one can make any changes without a specific, unique code. By doing this, you’re able to avoid banking scams.
-
Security Software
The last — but possibly most important — protective technology is quality, updatable security software on your mobile device or computer. Taking the precaution of installing security software ensures the utmost effectiveness of all other safeguards you put in place.
As you can see, technology is working towards making our account information more secure. By following a few simple steps, you’ll have a better shot at keeping your identity to yourself and staying safe from identity fraud.
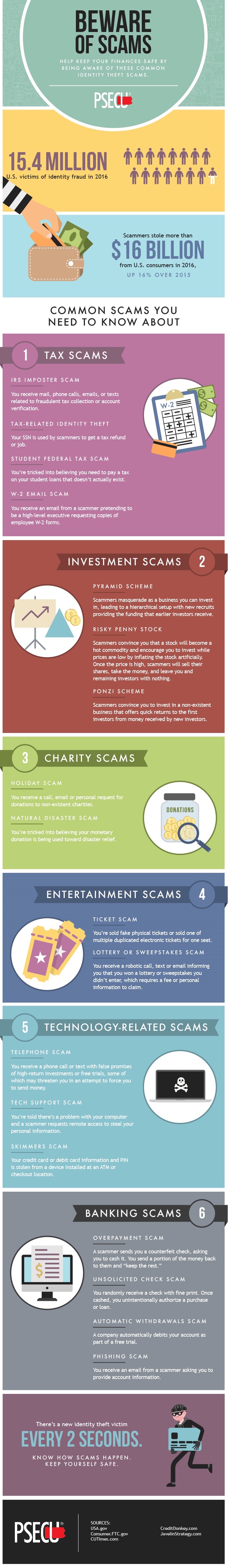
For more ways to protect yourself from identity fraud, check out this useful graphic from not-for-profit credit union PSECU!